China’s Red Menshen “sleeper cell” spies caught hiding deep inside global telecoms networks
Rapid7 uncovers "ongoing" espionage campaign involving long-term persistence within highly sensitive communications environments.

A mysterious China-linked threat actor called Red Menshen has spent years lurking inside the "backbone" of the world's communication systems, researchers from Rapid7 have revealed.
Described as "one of the stealthiest digital sleeper cells" the security firm has ever observed, the group appears to be dedicated to espionage against governments, critical infrastructure and private sector targets.
The research warns of a shift from opportunistic intrusion to deliberate, long-term persistence inside telecommunications networks, with threat actors aiming to stay undetected whilst collecting intelligence.
Rapid7 said it had identified a "broader pattern" among a range of telecom intrusions reported over the past decade that involved accessing call detail records, monitoring sensitive communications and exploiting trusted interconnections between operators.
"What looks like discrete breaches increasingly resembles a repeatable campaign model designed to establish persistent access inside telecommunications infrastructure," it wrote.
"Attackers are placing sleeper cells inside the telecom backbone: dormant footholds positioned well in advance of operational use."
Persistence, stealth and espionage
The "recurring elements" identified during the investigation include kernel-level implants, passive backdoors, credential-harvesting utilities, and cross-platform command frameworks, forming a "persistent access layer designed not simply to breach networks, but to inhabit them."
Raj Samani, chief scientist at Rapid7, said: "If you have access to telecommunications infrastructure, you are not just inside one company, you are operating close to the communication layer of entire populations, which makes this type of access highly valuable and elevates detection to a national-level concern.
"The activity we are seeing continues to evolve in ways that improve stealth and persistence, and organizations should treat detection as the start of investigation, not the end of it."
READ MORE: Phishing gangs are posing as government officials to steal money from permit applicants
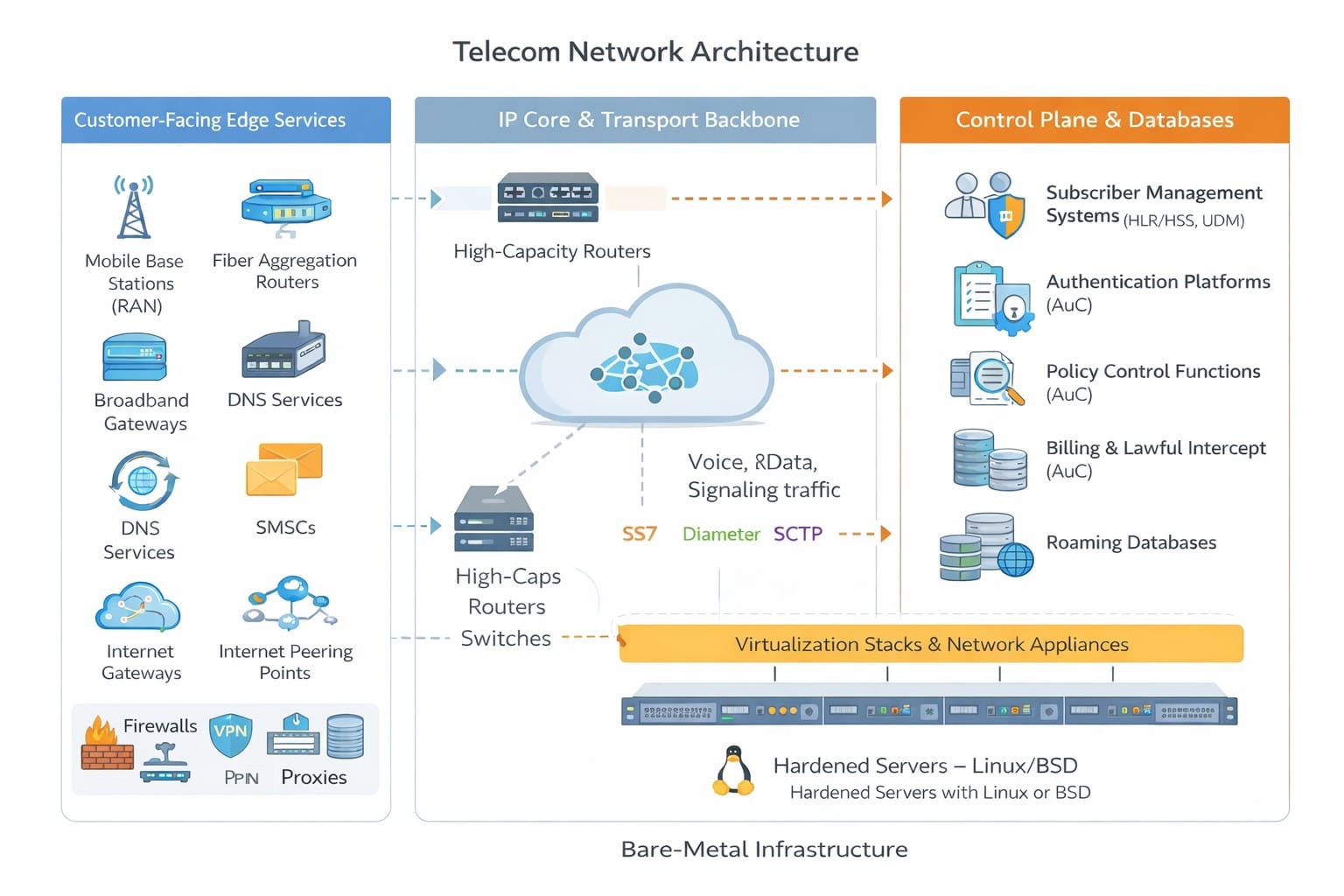
Modern telecom networks are complex, layered systems spanning identity, authentication, routing infrastructure, subscriber management, billing platforms, roaming databases and lawful intercept functions.
An attacker inside the telecom core could gain visibility into subscriber identifiers, signalling traffic, authentication exchanges, mobility events and communications metadata.
At its most serious, persistent access to this environment could enable sustained intelligence gathering, large-scale tracking of individuals, and the monitoring of sensitive communications involving high-value geopolitical targets.
“This is not traditional espionage; it is pre-positioning inside the infrastructure that nations depend on,” said Christiaan Beek, vice president of cyber intelligence at Rapid7. “We are seeing a persistent access model where attackers embed within core communications systems and maintain that access over extended periods.”
Backdoors and magic packets
The attackers were observed deploying BPFdoor, a stealthy Linux backdoor built to operate within the operating system kernel.
Rather than opening ports or calling home, it uses Berkeley Packet Filter (BPF) functionality to inspect network traffic directly, activating only when it receives a specially crafted trigger packet. There is no persistent listener, no beaconing and almost no visible footprint - effectively creating a hidden trapdoor embedded deep in the system.
Crucially, it operates at the same level as core system and hardware-facing functions inside what’s often described as the “bare metal” layer. By using legitimate packet-filtering mechanisms, its behaviour blends in with normal low-level network operations, making it extremely difficult to distinguish from routine infrastructure activity.
READ MORE: Cyberwar fears escalate as nation-state threat actors intensify private sector attacks
This forms part of a broader approach focused on deep infrastructure access. Rather than relying on conventional malware, attackers target bare-metal servers, virtualised systems and telecom core components, where they can remain embedded for long periods while avoiding detection.
The result is quiet, persistent access inside telecom networks, with visibility into communications as they move through the system - all while operating below the layers most security tools are designed to monitor.
Rapid7 wrote: “This approach represents a shift in stealth tradecraft. By positioning below many traditional visibility layers, the implant significantly complicates detection, even when defenders know what to look for.”
A history of BPFdoor
BPFdoor first emerged publicly around 2021, when researchers identified it in long-running espionage campaigns targeting telecom and government networks. Its source code was later reportedly leaked in 2022, lowering the barrier to entry for other threat actors.
At its core is a misuse of BPF, a legitimate mechanism used by tools such as tcpdump and libpcap to capture and filter network traffic before it reaches user-space applications.
The implant installs a custom BPF filter that scans incoming traffic for a specific pattern - a predefined sequence of bytes often referred to as a “magic packet”.
If that pattern is not present, the traffic passes through normally, with no visible service or indication that the system is compromised. When the correct sequence is delivered to the right destination, however, the implant activates instantly, creating a covert entry point without exposing itself to conventional detection methods.
READ MORE: US ban on Chinese routers leaves “millions” of insecure devices in American homes
Rapid7 added: "BPFdoor is far more than a stealthy Linux backdoor. The kernel-level packet filtering, passive activation through magic packets, masquerading as legitimate hardware management services, awareness of container runtimes, and the ability to monitor telecom-native protocols such as SCTP, point to a tool designed for deep infrastructure positioning.
"Rather than targeting individual servers, the operators appear to focus on the underlying platforms that power modern telecommunications networks... BPFdoor functions as an access layer embedded within the telecom backbone, providing long-term, low-noise visibility into critical network operations."
Read the full report and download a tool to identify variants of BPFdoor on the Rapid7 website.