FBI warns of surge in ATM jackpotting "cash on command" attacks
Criminals deploy Ploutus malware to infect cash machines and trick them into dispensing vast sums of money.
The FBI has warned of a sharp rise in ATM jackpotting attacks, in which criminals infect cash machines with malware and trick them into dispensing cash.
Threat actors are exploiting both physical and digital vulnerabilities to hijack ATMs, using malware from the Ploutus family and hardware devices to seize control of the machines.
The FBI said it has observed an increase in jackpotting incidents across the US since 2020. Since then, there have been roughly 1,900 ATM attacks, with 700 taking place last year alone resulting in losses of more than $20 million.
Ploutus malware exploits the eXtensions for Financial Services (XFS) software layer that controls an ATM.
When a legitimate transaction occurs, the ATM application sends instructions via XFS to the bank for authorisation. If a threat actor can issue their own commands to XFS, they can bypass bank security and instruct the ATM to dispense cash on demand.
The cash is not taken from customers' accounts - but stolen directly from the machine.
"As a result, Ploutus allows threat actors to force an ATM to dispense cash without using a bank card, customer account, or bank authorisation," the FBI warned.
"Once Ploutus is installed on an ATM, it gives threat actors direct control over the machine, allowing them to trigger cash withdrawals. Ploutus attacks the ATM itself, enabling fast cash-out operations that can occur in minutes and are often difficult to detect until after the money is withdrawn."
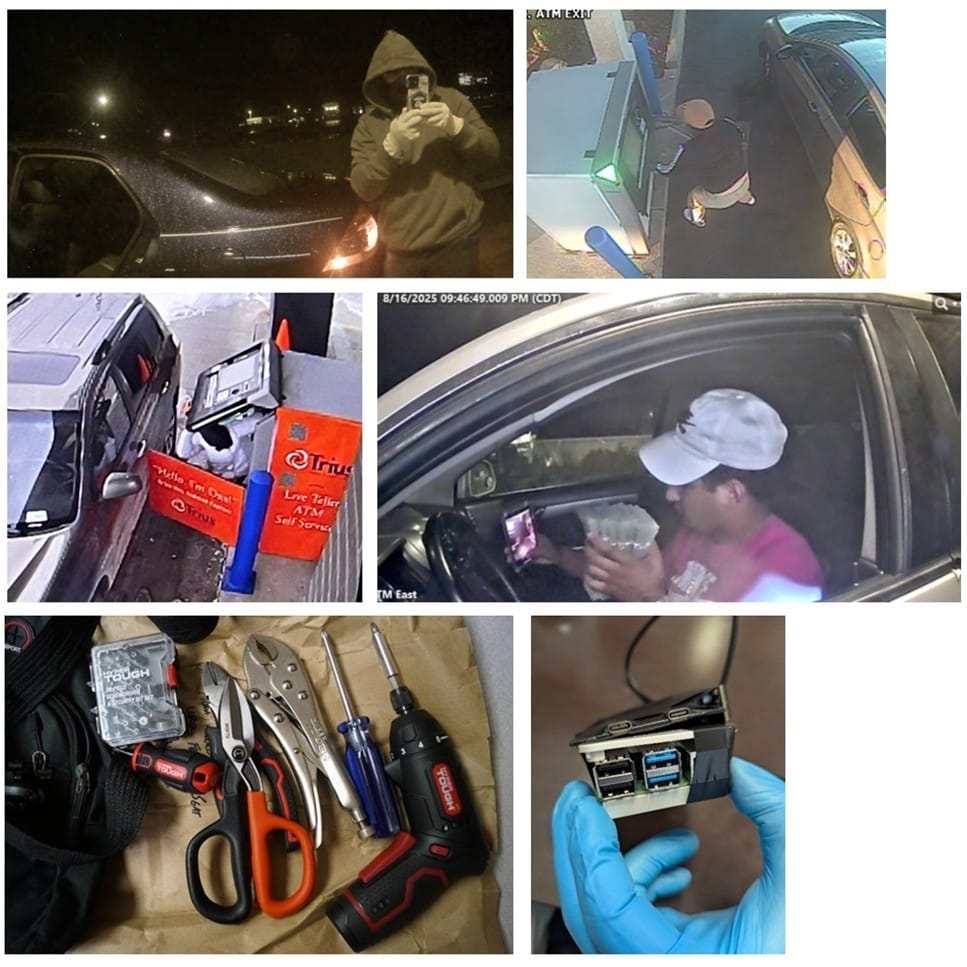
After the FBI issued its warning, a federal grand jury in Nebraska charged six Venezuelan nationals over a nationwide ATM jackpotting conspiracy that was allegedly linked to the Tren de Aragua gang, a designated Foreign Terrorist Organisation blamed for stealing more than $6 million from US banks.
Shake down that moneymaker
Attacks often start by literally opening an ATM using generic keys that are "widely available", according to the FBI.
Threat actors can then remove the ATM’s hard drive, connect it to their computer, upload malware and then reconnect the drive before rebooting.
Sometimes they replace the hard drive with an external device preloaded with malicious software.
The FBI wrote: "The malware interacts directly with the ATM hardware, bypassing any communications or security of the original ATM software. The malware does not require a connection to an actual bank customer account to dispense cash.
"The malware can be used across ATMs of different manufacturers with very little adjustment to the code, as the Windows operating system is exploited during the compromise."
READ MORE: Dark pool trading is casting a shadow over market stability, researchers warn
Unfortunately, until banks find a reliable way to mitigate attacks, they are likely to continue and even get worse.
Dray Agha, senior manager of security operations at Huntress, said: "Criminals are using malware like Ploutus to bypass the bank's verification system entirely, forcing the machine to dole out cash on command. The $20 million stolen last year proves that the security layer controlling the ATM's hardware is now a primary target.
"For financial institutions, this is a wake-up call to treat every ATM like an endpoint on their network, not just a standalone safe. These attacks can be over in minutes and often go unnoticed until the cash is gone because the malware doesn't trigger the usual bank-side transaction checks.
"Proactive monitoring for unauthorised physical access to the machine's interior, combined with stronger logical access controls for software updates, is critical to stopping these 'phantom withdrawals.'"
Like shoplifting, ATM jackpotting may sound like a victimless crime. It might even seem attractive to many of us, because who wouldn't want a cash machine to spit out tons of free money?
But, as ever, it will be poor people who are impacted most by a rise in ATM crime. Just as the cost of theft in stores is passed on to consumers, a surge in jackpotting could disproportionately affect deprived or rural areas where cash access is limited if banks choose to close at-risk or unprofitable machines.
How banks can tackle jackpotting
The FBI banks and ATM operators to adopt targeted audit policies to detect and prevent jackpotting attacks, particularly those involving the Ploutus malware family.
Rather than relying solely on network monitoring, the bureau recommended closely tracking removable storage use, file access, and new process creation - measures designed to flag the early stages of physical intrusion and malware deployment with minimal impact on system performance.
The guidance placed heavy emphasis on physical security. Operators are advised to install vibration and temperature sensors, upgrade standard locks that could be bypassed with widely available keys, and add alarm-triggering keypads to maintenance hatches.
Additional barriers protecting cashboxes, along with properly positioned security cameras and preserved footage, were also recommended to deter and document attacks.
READ MORE: Dark web cybercriminals vow to fight on after FBI seizure of Ramp forum
On the hardware and software side, the FBI called for automatic shutdown mechanisms when indicators of compromise are detected, as well as strict device and software whitelisting to prevent unauthorised hardware, such as USB drives, from being connected.
Firmware integrity checks using Trusted Platform Modules, full disk encryption, memory integrity protections and component tracking through software and hardware bills of materials were all highlighted as ways to harden machines against tampering.
The bureau recommended enabling detailed auditing of USB insertions, file system changes, and process creation events, allowing security teams to correlate suspicious activity such as a USB device being inserted, malware copied and executed, and logs subsequently cleared. Long retention periods and centralised log storage were encouraged to support forensic investigations.
The alert also urged regular auditing of ATM configurations, the removal of default credentials, pre-production security testing, IP address whitelisting, and the deployment of endpoint detection and antivirus tools. Finally, it stressed the importance of information sharing across the industry and staff training to improve readiness and response speed as jackpotting techniques evolves.
Get the full indicators of compromise here.




