Cyberwar fears escalate as nation-state threat actors intensify private sector attacks
Leaders report growing concerns that attacks from adversary nations could "cripple critical infrastructure".

British organisations have reported a rise in suspected nation-state cyberattacks, as security leaders warn that geopolitical tensions are spilling into the private sector.
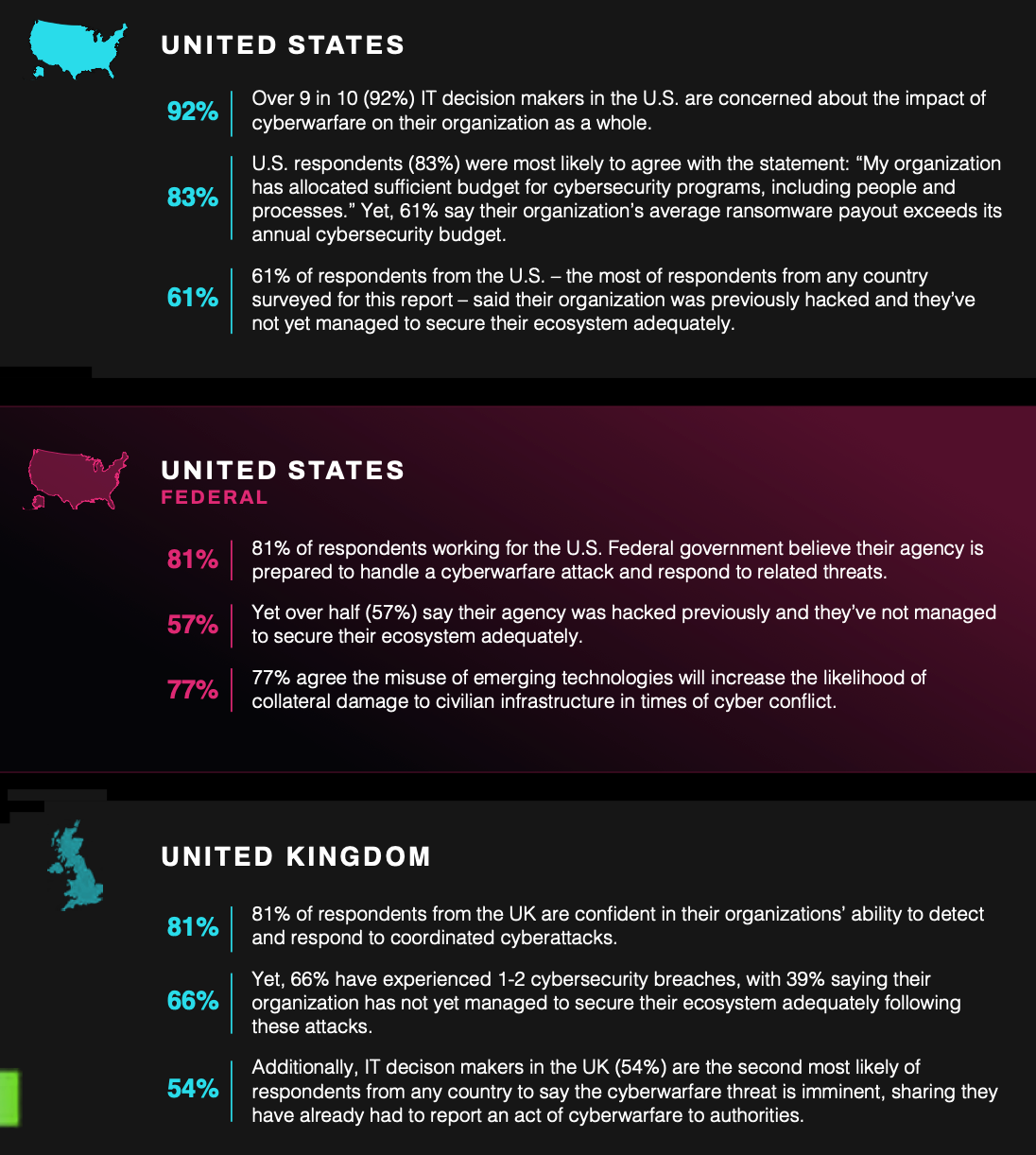
A new survey from Armis found that 54% of organisations have come under attack from state-linked hackers and reported these incidents to authorities - up from 47% last year.
The research also found that 92% of UK IT decision makers are now concerned about the impact of cyberwarfare on their organisations.
“Cyberwarfare has moved from a distant geopolitical issue to a day-to-day business risk for UK organisations”, said Marc Jones, Regional Director, UK & Ireland at Armis.
“When businesses are changing suppliers and reallocating budgets in response to geopolitical instability, it signals a shift from growth to defensive posture.
"The organisations that will navigate this successfully are those that move from reactive security to actively understanding, prioritising and reducing their cyber exposure before threats materialise."
Companies on the front line of cyberwar

Armis Labs’ fourth annual global Cyberwarfare report, A World Under Pressure: Cyberwarfare in an Age of AI-Fueled Escalation, found that 76% of UK tech leaders fears that nation-state actors have the capabilities to “instigate a full-scale cyberwar that could cripple critical infrastructure worldwide.”
Just over one third (39%) admitted they had previously been attacked and had still not adequately secured their environments. Additionally, 46% said cyberwarfare concerns had delayed, stalled or stopped digital transformation projects, slowing innovation efforts across UK organisations.
The survey also found that geopolitical instability is “further intensifying risks”, with 80% of UK respondents reporting that tensions between states have increased the threat of cyberwarfare, up from 74% in 2025. Three-quarters said they were reconsidering suppliers and increasing cybersecurity investment as a direct result.
“Cyberwarfare is now a constant condition,” said Nadir Izrael, CTO and Co-Founder of Armis. “Attackers are operating at machine speed, while too many organisations are still trying to defend themselves with assumptions and structures built for a very different threat landscape.
“Nation-state capabilities, AI acceleration and unresolved security gaps are converging. For many organisations, it’s not a matter of if they’ll face a cyberwarfare attack, but when - and how truly prepared they are to defend themselves and protect their environment when it happens.”
The 2026 Armis Cyberwarfare Report is based on a study of more than 1,900 global IT decision-makers, including 500 respondents from the UK. Read it here and check out its US and UK findings below.
READ MORE: President Trump unveils new Cyber Strategy that's big on bluster, but light on detail
How would we know a cyberwar had started?
Cyberwar rarely begins with a single visible event. Unlike conventional conflict — where hostilities are marked by troop movements or missile strikes — cyber operations often unfold quietly, long before governments formally acknowledge a state of war.
Digital espionage, infrastructure probing and targeted intrusions can continue during both periods of tension and apparent peace. Attribution also remains difficult, as attackers frequently use proxies, criminal networks or compromised infrastructure to obscure responsibility.
In an earlier interview, we asked Michael Freeman, head of threat intelligence at Armis, how we would know if a cyberwar had begun.
READ MORE: From zero days to zero hours: How AI is accelerating attacks to "machine speed"
“One way I look at it is through the example of the US National Security Agency,” Freeman told us. “The NSA publicly ran a programme known as Tailored Access Operations, which was essentially an offensive cyber campaign. It was modelled in a very similar way to Israel’s Unit 8200 [an elite IDF cyberwar and intelligence unit]. At various points, through leaks by different sources, it was described as the most effective intelligence-gathering programme the NSA had ever operated.
“When you compare that to more traditional intelligence work – such as the CIA putting boots on the ground, recruiting assets, and running human intelligence operations – the contrast is stark. Assembling a 20-person team to target individuals in another country, identify potential recruits, and turn them can take years and requires enormous time and effort.
Hacking into their phones is much faster, but in most countries would be considered an act of war, because you are overtly targeting another state in a very direct way.”




