The second coming of Shai-Hulud: Malware goes open-source, evolves in the wild
“The scale and speed of the spread resemble some of the most disruptive supply chain incidents we have seen in recent years."

The threat actor TeamPCP has open-sourced its notorious Shai-Hulud worm, spawning a new wave of variants on GitHub.
Described as the “second coming” of the malware, the latest mini version of Shai-Hulud has already been forked dozens of times, escalating into a sprawling supply-chain campaign affecting at least 373 malicious package versions across 169 npm packages, including TanStack, Mistral, UiPath and Squawk.
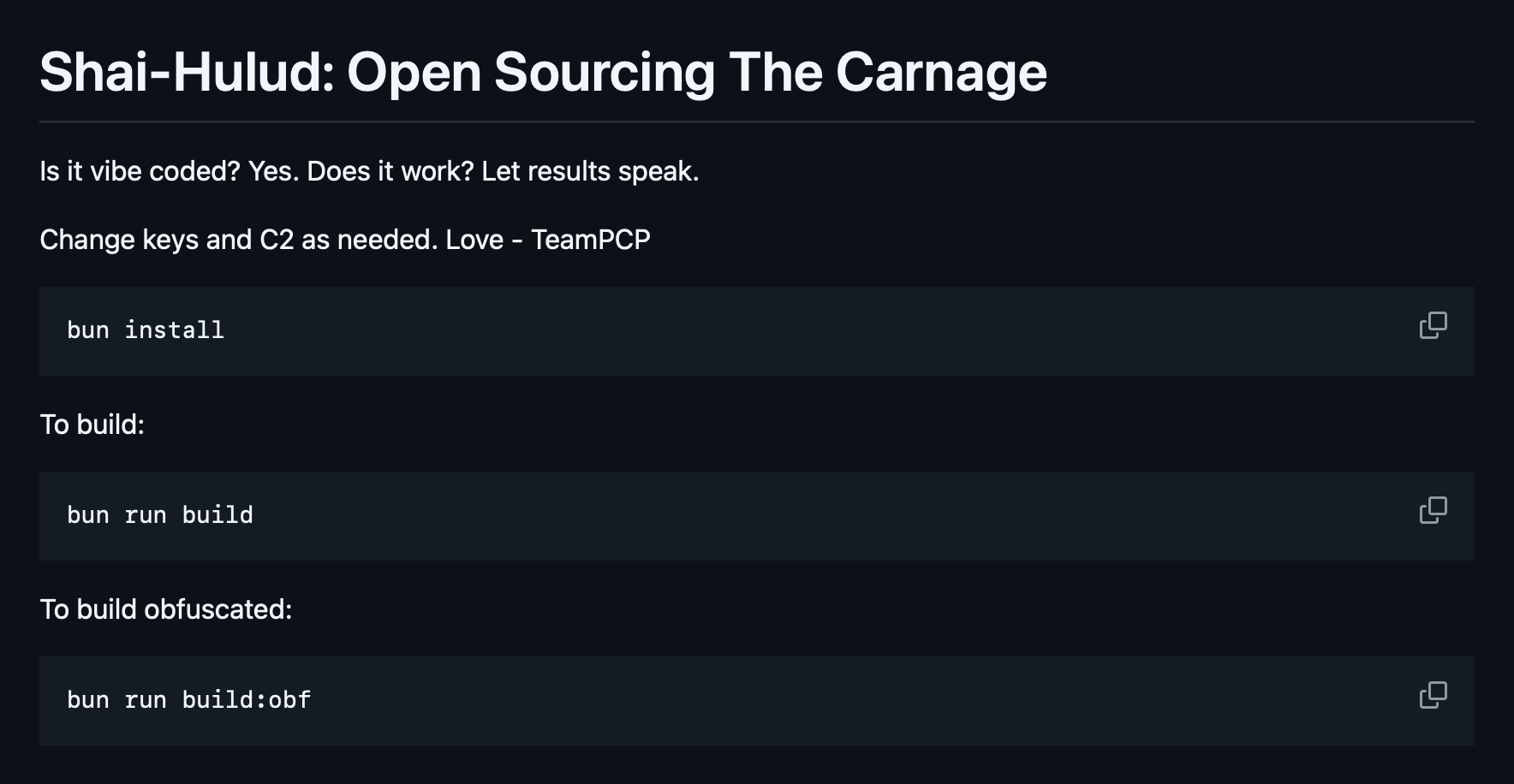
On GitHub, TeamPCP said it was "open sourcing the carnage" and wrote: "Is it vibe coded? Yes. Does it work? Let results speak."
The worm is designed to steal developer and CI/CD credentials, then use them to compromise additional packages and propagate further through the software supply chain, security researchers said.
"Mini Shai-Hulud has moved from a smaller SAP-focused incident into a broader npm supply-chain attack," warned Raphael Silva of Aikido.
"The important lesson is not just that more packages were compromised. It is that the malware is built around the way modern release systems work."
The return of Shai-Hulud
Shai-Hulud targets GitHub and npm tokens, AWS credentials, Kubernetes service account tokens, environment variables and local secrets. Stolen publishing rights can then be abused to modify package archives, inject malicious dependencies, bump versions and push infected releases.
The malware also appears designed to evade scrutiny. Researchers observed it adding hooks to Anthropic’s Claude Code that execute when the AI coding tool starts, while the GitHub repository contains an “Anthropic Magic String” - text intended to prevent Claude Code from analysing the profile.
“Someone doesn’t want AI eyes on their work,” wrote Moshe Siman Tov Bustan, a researcher with Ox Security.
Other obfuscation tactics include GitHub commits dated January 1, 2099.
“TeamPCP isn’t just hiding their tracks - they’re hiding them in the future,” Bustan added.
Ox also warned that "the copycats are already here", advising that "independent threat actors have already begun modifying Shai-Hulud and expanding its reach".
"Echoes of Log4j"
Check Point said the Shai-Hulud 2.0 campaign began when attackers compromised or published malicious npm packages that executed payloads during npm’s preinstall phase.
This allowed the code to run before installation completed - and even if installation later failed - giving attackers early access to developer machines, CI/CD pipelines and build environments.
Between 21 and 23 November 2025, the campaign spread rapidly across the npm ecosystem, compromising hundreds of packages and more than 25,000 GitHub repositories within hours.
Check Point later confirmed large-scale exposure of developer and cloud credentials, including 775 GitHub tokens, 373 AWS credentials, 300 Google Cloud credentials and 115 Azure credentials.
Researchers say the campaign marks a significant evolution in supply-chain attacks because it weaponises modern software delivery infrastructure itself.
READ MORE: Nation-state actors now behind majority of serious UK incidents, NCSC security chief warns
The worm abuses trusted publishing systems, automated propagation and CI/CD workflows to spread through development pipelines at machine speed.
Adi Bleih, Security Researcher, External Risk Management, at Check Point, said: “Shai-Hulud 2.0 is a highly coordinated supply chain attack with an unusually aggressive execution chain.
“This type of incident demonstrates how a single dependency can become a direct pathway into CI/CD systems and cloud environments.
“The scale and speed of the spread resemble some of the most disruptive supply chain incidents we have seen in recent years, and it carries echoes of the widespread ripple effects seen during Log4j.
“Organisations should act immediately by auditing dependencies, rotating all potentially exposed secrets and securing their build pipelines.”
Nigel Douglas, Head of Developer Relations at Cloudsmith, said the self-propagating attack published more than 84 malicious artefacts across 42 TanStack packages.
“The clock started the moment they hit the registry, not the moment they were pulled,” Douglas said.
“At 12 million weekly downloads, the exposure window doesn’t need to be wide to hurt organisations.
READ MORE: fast16 exposed: Cyber sabotage malware first teased in NSA leaks could be older than Stuxnet
“Even if organisations are unsure if they have been compromised, the immediate step is to audit any build that ran today against the npm registry pulling tanstack packages.
“Beyond incident response, organisations should configure their systems to wait before automatically adopting newly published software at the very minimum. This 24-48h buffer gives the security community time to catch anything malicious before it reaches internal infrastructure.
“The software supply chain runs on trust relationships that were never designed with this threat model in mind. Developers trust package namespaces because those namespaces have a track record, but a compromised publish token or stolen CI/CD secret can weaponise that trust instantly.”




